How Agentic AI Detects and Responds to Cyber Threats in Real Time

Written by Matthew Hale
- What Is Agentic AI and Why It Matters for Cybersecurity
- How Agentic AI Detects Cyber Threats
- How Agentic AI Responds to Threats Automatically
- Real-World Agentic AI Use Cases in Cyber Defense
- How Agentic AI Reduces Attack Dwell Time
- Building Cyber Resilience with Agentic AI
- Developing Skills for AI-Driven Security Operations
- The Future of Agentic AI in Cybersecurity
In early 2026, Google closed down the IPIDEA proxy network after realizing that millions of smartphones and PCs had been secretly hijacked to launch massive automated cyberattacks.
This is what the state of cybersecurity looks like today. Attackers can gain access to systems, elevate their privileges, and exfiltrate data out the door in minutes, often before human teams even have a chance to respond. As automation and AI-powered attacks continue to accelerate, human-driven security operations are getting left in the dust.
Agentic AI changes this balance. By understanding how agentic AI works, organizations can deploy autonomous systems that detect, investigate, and respond to threats in real time. This blog explains how agentic AI works in cybersecurity, with practical agentic AI use cases, agentic AI workflows, and real-world agentic AI examples that enable machine-speed defense.
What Is Agentic AI and Why It Matters for Cybersecurity
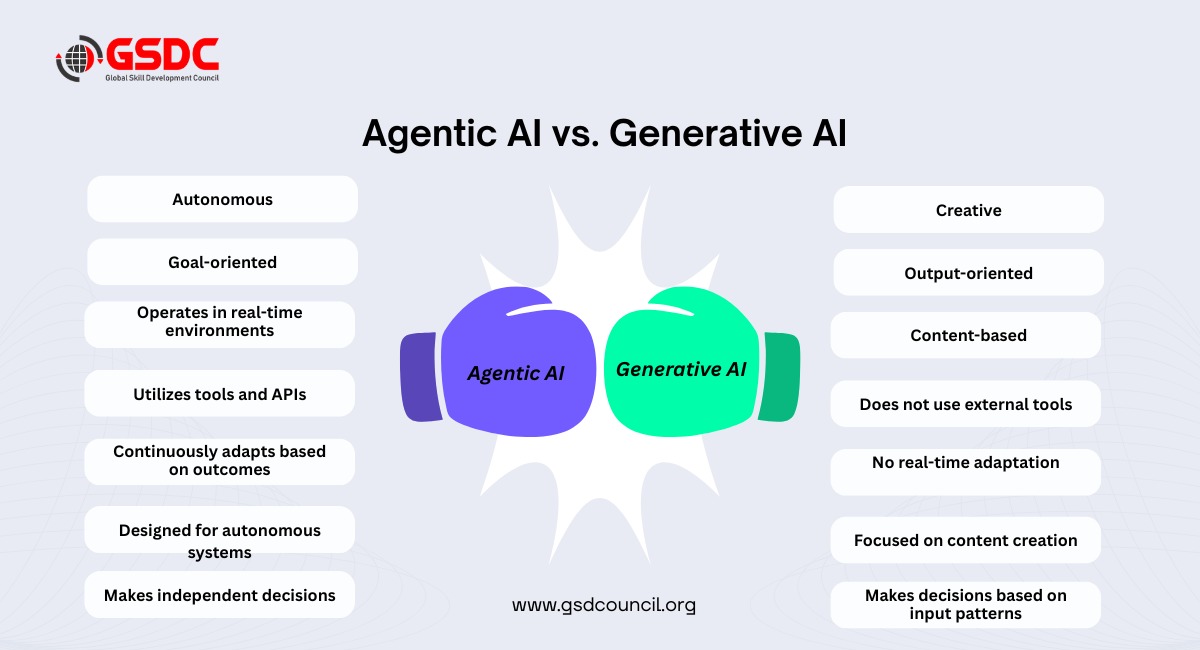
Agentic AI refers to systems that operate with independent agency, meaning they can observe, reason, and act on security environments to achieve specific goals.
To understand agentic AI how it works, it is necessary to compare it with traditional automation. Unlike traditional automation solutions, agentic AI systems are always connecting signals from identity, endpoint, network, and cloud layers and making decisions on the best course of action independently.
This shifts the focus of security from reacting to alerts to securing outcomes, which means minimizing actual risk.
How Agentic AI Detects Cyber Threats
Understanding how agentic AI works in threat detection explains why it is more effective than traditional, signature-based security models.
- Identifying Suspicious and Anomalous Behavior
Rather than relying solely on established attack patterns, agentic AI is constantly learning what constitutes typical user, device, and workload behavior. When something unusual occurs, such as an unusual login attempt, an unexpected data transfer, or an unexpected change in permissions, it is identified as a possible threat, even if no known malware is present.
This is a key difference when comparing gen AI vs agentic AI. While generative AI focuses on content creation, agentic AI reasons over behavior and intent to detect emerging threats.
- Connecting Signals Across Multiple Systems
Modern attacks are much less likely to show themselves through a single system. Agentic AI correlates between signals originating from identity, endpoint, network, cloud, and application layers, which enables agentic AI to detect low-and-slow attacks that other tools may not see.
- Automatically Confirming Genuine Threats
Agentic AI is automatically able to collect evidence, verify indicators, and evaluate risk levels. This allows for the minimisation of false positives, speeding up triaging, and only firing response mechanisms when verified threats are actually present.
Together, these capabilities significantly improve mean time to detect (MTTD) while reducing analyst workload. As organizations move toward autonomous security operations, institutions like Global Skill Development Council (GSDC) play a key role in helping professionals build practical skills in agentic AI and next-generation cybersecurity.
How Agentic AI Responds to Threats Automatically
Detection alone is no longer sufficient. The true value of agentic AI lies in its ability to respond without waiting for human intervention.
It supports a closed-loop security strategy with intelligent, agentic processes that integrate finding, testing, and responding to threats seamlessly. After authenticating a plausible threat, the system can respond independently to:
- Isolate the affected devices or cloud workloads
- Prevent malicious network activity
- Suspend or reset compromised identities
- Enforce more robust authentication
- Implement containment and access policies
- Initiate recovery or rollback procedures
These processes occur in seconds, greatly reducing an attacker’s lateral movement, privilege escalation, or data exfiltration.
Most importantly, agentic AI processes are governed by policies, confidence thresholds, and human review. High-risk actions require human approval, and low-risk actions with high confidence are performed automatically, finding a balance between speed and control.
Real-World Agentic AI Use Cases in Cyber Defense
To understand operational impact, it helps to look at real-world agentic AI use cases and agentic AI examples in cybersecurity environments.
- Detect & Contain Ransomware
Use agentic AI to detect abnormal file-level encryption, correlate endpoint and identity anomalies, and automatically isolate compromised systems. Agentic AI terminates malicious processes, restricts credentials, blocks lateral movement, and often prevents the widespread encryption of data due to ransomware attacks.
- Identity-Based Attacks and Account Takeover
When anomalous login behavior is detected, agentic AI correlates identity, endpoint, and network signals to assess session risk. Step-up authentication is enforced, high-risk sessions are suspended, and access is restricted to prevent credential abuse.
- Insider Threat and Privilege Abuse
Agentic AI continuously monitors privileged user behavior and detects deviations from normal access patterns. Elevated privileges can be limited automatically, investigative workflows triggered, and evidence preserved with full audit visibility.
- Cloud and Hybrid Environment Threats
In hybrid environments, agentic AI detects anomalous cloud workload behavior, misconfigurations, and cross-environment lateral movement. Compromised resources are isolated, access policies updated, and rollback processes initiated.
- Phishing-Led Intrusions
Agentic AI correlates suspicious email activity with endpoint and identity behavior. If malicious execution occurs, endpoints are isolated and lateral movement attempts are blocked - preventing escalation.
These agentic AI examples demonstrate how security operations evolve from alert-driven response to proactive, machine-speed defense.
How Agentic AI Reduces Attack Dwell Time
Attack dwell time is one of the primary indicators of attack impact. While there have been advancements in detection technology, most organizations still require an average of 181 days to discover that they have been attacked and even longer to contain the attack. Thus, this gives attackers an excessive amount of time to remain on-site before the establishment of defence.
By shortening the conventional security Lifecycle, Agentic AI decreases dwell time:
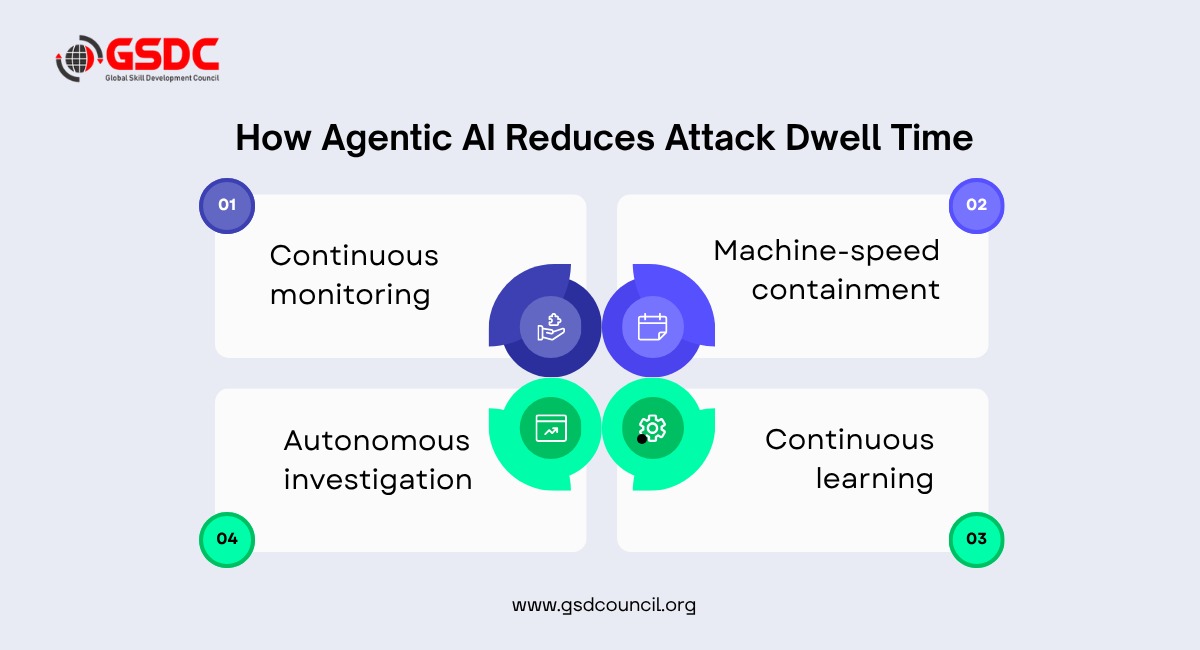
- Continuous monitoring decreases detection time by evaluating the behavioral actions of users, endpoints, networks, and in the cloud.
- Autonomous investigation eliminates manual delays by automatically collecting evidence, correlating signals, and confirming threats.
- Machine-speed containment inhibits the persistence of attackers by isolating the malicious system, limiting the identity of the attackers, and disabling the malicious activity in a matter of seconds.
- Continuous learning as a result, organizations can minimize exposure from hours or days to minutes or even seconds, thus greatly reducing the severity of the breach and costs of recovery.
As a result, organizations can minimize exposure from hours or days to minutes or even seconds, thus greatly reducing the severity of the breach and costs of recovery.
As security operations shift toward autonomous, machine-speed defense, professionals increasingly need the skills to design, govern, and oversee these systems. The Agentic AI Professional Certification helps practitioners build practical expertise in agentic AI workflows, autonomous threat detection, and real-time response.
Building Cyber Resilience with Agentic AI
Cyber resilience requires more than speed - it demands adaptability and continuous improvement. Modern agentic AI frameworks support this by enabling:
- Learn continuously from emerging attack scenarios
- Enforce security policies consistently throughout every environment
- Provide scalability of defence capabilities across distributed and hybrid multi-cloud infrastructures
- Provide automated containment and restoration to ensure uninterrupted business operations.
These models create a positive feedback loop, where each attack makes the next one more secure.
Developing Skills for AI-Driven Security Operations
The global talent gap in cybersecurity is expanding, with approximately 4.8 million cybersecurity talent vacancies going unfilled. This talent gap makes it difficult for organizations to rely solely on human-driven security as threats continue to rise and become increasingly automated in their development.
Security experts need to start thinking about designing, governing, and managing AI decision-making systems using their own skills and knowledge to develop autonomous SOCs, which are becoming more common.
This has led to the increasing need for agentic AI Certification. Organizations such as the Global Skill Development Council (GSDC) are helping organizations to use agent-based AI responsibly through Agentic AI Professional Certification.

The Future of Agentic AI in Cybersecurity
As attackers embrace automation and AI, the cybersecurity community must keep pace – and better yet, stay ahead of the curve. Agentic AI represents a shift from security that is human-tempo-driven to machine-driven and intelligent.
Organizations can reduce dwell time, increase resilience, and protect against next-generation threats by understanding how agentic AI works, capitalizing on existing agentic AI use cases, and embracing sound agentic AI frameworks.
To succeed, it takes more than technology – it also takes talented people, strong governance, and maturity. The early adopters of agentic AI will build the future of cybersecurity, while others may find themselves playing catch-up at human speed to threats that are machine-driven.
Related Certifications
Stay up-to-date with the latest news, trends, and resources in GSDC
If you like this read then make sure to check out our previous blogs: Cracking Onboarding Challenges: Fresher Success Unveiled
Not sure which certification to pursue? Our advisors will help you decide!