PCI DSS Requirements Explained: A Simple Guide to the 12 Essentials
Written by Matthew Hale
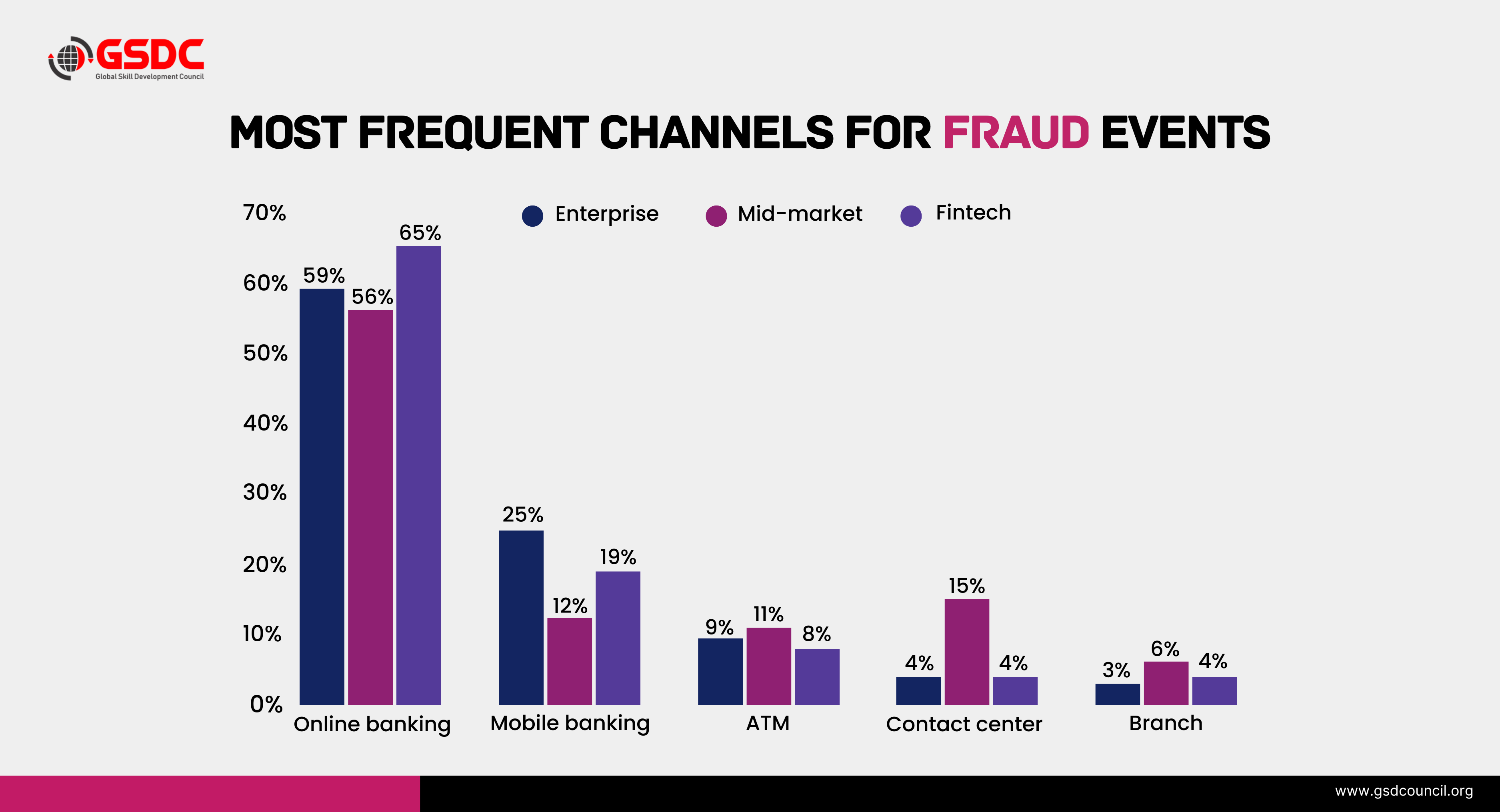
Any business that accepts card payments handles sensitive financial information. This data must be protected at all times to prevent fraud, breaches, and misuse. The demand for robust security measures has been exacerbated by the increase of payment fraud on a global scale.
Recent reports reveal that global credit and debit card fraud losses are anticipated to be around $48 billion by the end of 2025, which is an increase from the figure of approximately $40 billion in 2024.
This growing trend highlights why stronger, more consistent security standards are essential in today’s digital payment landscape.
What is PCI DSS?
The Payment Card Industry Data Security Standard (PCI DSS) is a global framework that protects cardholder data wherever it is stored, processed, or transmitted. The latest version, PCI DSS 4.0, strengthens security through continuous monitoring, risk-based controls, and improved authentication. At its core are 12 PCI DSS requirements that help organisations create and maintain secure payment environments.
This PCI DSS blog breaks these essentials down in a simple, practical way.
What Are PCI DSS Requirements?
PCI DSS requirements are a set of security measures that keep cardholder data safe from the time it is created until the time it is destroyed.
- Take payments by card
- Keep cardholder information
- Handle payment transactions
- Send card information
Understanding the rules for PCI DSS compliance makes payment environments safer and lowers the chance of breaches. A PCI DSS compliance checklist is used by many businesses to keep an eye on and check their controls all the time.
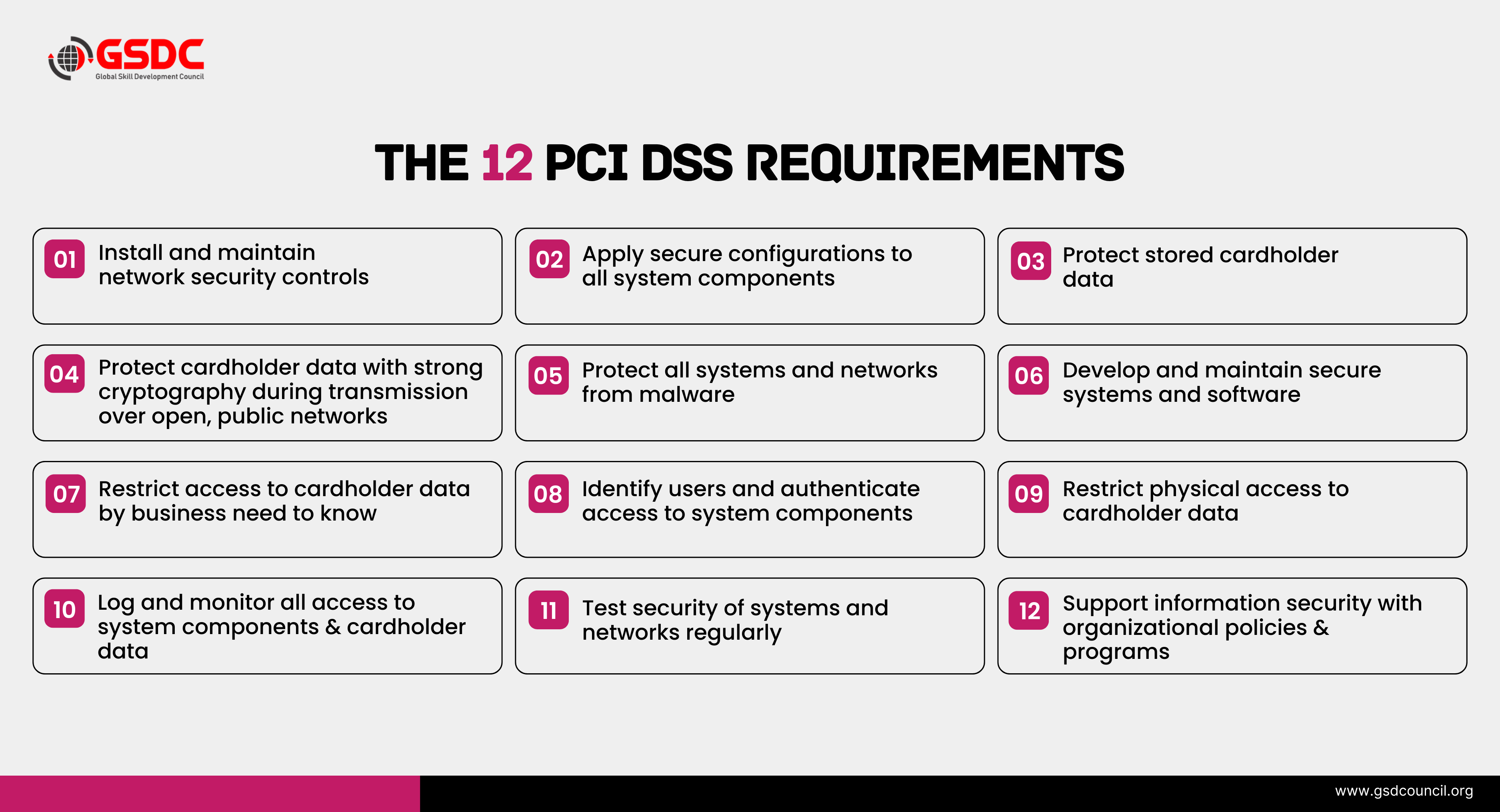
The 12 PCI DSS Requirements
Following are the core PCI DSS rules referenced in most PCI DSS guides and compliance checklists.
1. Protect Networks with Firewalls
To protect systems that store or process cardholder data, organisations must set up, configure, and keep firewalls up to date. Firewalls keep out unwanted traffic and stop people from getting in.
For example, a store uses a firewall to stop all outside traffic except for connections from its payment processor that have been approved.
2. Do Not Use Default Passwords or Settings
Default passwords and vendor-supplied configurations must be changed before systems go live.
For example, before deploying a new router, an organisation changes the default admin username and password and disables unnecessary default services.
3. Keep cardholder data safe
Data about cardholders must be encrypted, masked, tokenised, or cut off. One should never keep sensitive authentication data after it has been provided.
For example, a hotel system keeps only the last four digits of a credit card number and replaces the rest with a secure token.
4. Encrypt Cardholder Data During Transmission
When data is transmitted over open or public networks, it must be encrypted using modern cryptographic protocols.
For example, an e-commerce site uses HTTPS/TLS 1.2+ to make sure that payment information is sent safely during checkout.
5. Protect Systems From Malware
Anti-malware tools must be deployed, updated, and monitored to detect harmful software.
For example, A payment server runs automated daily malware scans and sends alerts when suspicious files are detected.
6. Keep malware out of systems
For the detection of harmful software, anti-malware tools need to be installed, updated, and monitored.
For example, A payment server runs automated malware scans every day and sends alerts when it finds files that look suspicious.
7. Limit access to only those who need it for business reasons.
People who need to see cardholder data for their jobs should be the only ones who can.
For example, customer service representatives can see a customer's transaction history, but they can't see their full credit card numbers.
8. Give each user a unique ID and use strong authentication.
Each user must have a unique ID, and strong authentication methods, like MFA, must be used.
For example, employees use unique usernames and MFA through a mobile authenticator to log into the cardholder data environment.
9. Limit Physical Access to Cardholder Data
Individuals who are authorised to perform certain tasks only should be allowed to have physical access to the facilities where systems holding cardholder data are located.
For example, The tightly controlled data center is only accessible through biometric access control, keycards are required for entry, and visitor logs are maintained to keep track of the people who go into the server room.
10. Track and Monitor All Access
Any access to system components and cardholder data must be recorded and checked.
For example, A security dashboard in real time records all attempts to log in, changes, and failed authentications and notifies the security team.
11. Regularly Test Security Systems
Security controls should be verified through vulnerability scans, penetration tests, and continuous monitoring.
For example, An external security firm conducts a yearly penetration test of the payment environment to identify security loopholes.
12. Maintain an Information Security Policy
A well-defined, current information security policy should serve as a framework that sets out the requirements, roles, and responsibilities for the protection of cardholder data.
For example, Employees attend annual PCI DSS training and sign a policy agreement which specifies the secure handling of cardholder information.
Understanding the 12 PCI DSS requirements is necessary; however, putting them into practice effectively demands on-the-job experience and should be backed by a credential such as the Certified PCI DSS (Payment Card Industry Data Security Standard) certificate.
PCI DSS Compliance Toolkit 🔐
Why is PCI DSS important?
PCI DSS is important because it creates a strong, consistent security framework that protects payment data at every stage of its lifecycle. Rather than relying on a single control, it reinforces multiple layers of defence so organisations can process card payments securely and confidently.
The Payment Card Industry Data Security Standard strengthens key areas such as:
- Network security – preventing unauthorised access to critical systems
- Cardholder data protection – keeping sensitive information encrypted, masked, or tokenised
- Access controls – ensuring only authorised individuals can view or handle cardholder data
- Logging and monitoring – helping teams identify unusual or suspicious activity quickly
- Testing and governance – confirming that security controls continue to work as intended
Together, these elements form a complete security ecosystem that supports safe and reliable payment operations.
By meeting PCI DSS compliance requirements, organisations can:
- Reduce the risk of fraud and data breaches
- Strengthen protection against cyberattacks targeting payment environments
- Avoid penalties, legal issues, and reputational damage
- Build long-term trust with customers and partners
PCI DSS Compliance Is an Ongoing Process
Being compliant cannot be confirmed during a single audit. In fact, PCI DSS 4.0 stresses the need for continuous monitoring, frequent changes, keeping records, and employee training.
An organisation's PCI DSS compliance checklist that is well-planned enables them to follow the controls over a period when both technology and threats change.
Industry-led learning bodies such as GSDC play a vital role in helping the different professionals maintain their knowledge and skills in line with the changes of PCI DSS compliance requirements.Building Expertise in PCI DSS Compliance
One of the main factors that lead to the effective execution of PCI DSS requirements is a group of qualified professionals having a thorough understanding of both the technical and operational sides of compliance. In order to facilitate this, the Global Skill Development Council (GSDC) provides the Certified PCI DSS (Payment Card Industry Data Security Standard) credentials which is the formal title of the Payment Card Industry Data Security Standard Certification.
This certification enables the professionals to:
- Grasp the concept of PCI DSS together with its functionality
- Carry out PCI DSS requirements in actual situations
- Employ PCI DSS compliance checklists as a tool for continuous internal audits
- Get ready for PCI DSS 4.0 evaluations
The main target of this training is:
- Security analysts
- IT administrators
- Risk and compliance professionals
- Auditors and consultants
As payment security is turning out to be a global concern, certified PCI DSS holders are highly sought after and can find opportunities in the sectors of banking, fintech, e-commerce, retail, and service providers.
Final Thoughts
Understanding PCI DSS requirements is essential for protecting the trust behind every digital transaction. When a company complies with the Payment Card Industry Data Security Standard, it is in a position to protect the cardholder data, minimize the occurrences of security breaches, and at the same time, keep the customer loyalty for a long period of time.
In an increasingly digital and threat-driven world, strong PCI DSS knowledge has become a critical capability for anyone involved in cybersecurity, compliance, or payment operations. It supports better decision-making, enhances security practices, and helps organisations maintain a secure and reliable payment environment.
Related Certifications
Stay up-to-date with the latest news, trends, and resources in GSDC
If you like this read then make sure to check out our previous blogs: Cracking Onboarding Challenges: Fresher Success Unveiled
Not sure which certification to pursue? Our advisors will help you decide!