If you haven’t defined your risk appetite, your attackers will
Written by Kassandra Jaramillo Calvo
- What Is Information Security Risk Appetite?
- Why ISO/IEC 27001 Alone Is Not Enough
- Risk Appetite is a Leadership Decision
- Risk Appetite vs Risk Capacity
- How ISO/IEC 27001 Supports Risk Appetite
- Key Areas Where Risk Appetite Should Be Defined
- Turning Risk Appetite Into Action
- Common Mistakes to Avoid
- Strengthen Your Risk Leadership
- Conclusion
Most organizations don’t get breached because they lack controls. They get breached because no one clearly defined what risk was acceptable in the first place. This is not a story about compliance, it’s about how organizations unknowingly accumulate risk even when they’re fully certified.
ISO/IEC 27001 is implemented, audits are passed, and controls are in place, yet exposure continues to grow, not because security is failing, but because decisions are being made without clear boundaries. Every day, organizations make trade-offs between speed and security, convenience and control, delivery and assurance, and in doing so, they are defining their real risk appetite, often without realizing it.
When risk appetite isn’t explicitly defined, it doesn’t disappear; it’s silently assumed, inconsistently applied, and gradually accumulated. ISO/IEC 27001 provides structure, but structure alone isn’t enough. Without clearly defined boundaries, security becomes reactive, exceptions become normalized and risk is no longer governed, it’s inherited. And in the gap between what is controlled and what is tolerated, attackers operate. Because they don’t exploit controls, they exploit uncertainty.
What Is Information Security Risk Appetite?
Information security risk appetite is the amount and type of cyber risk an organization is willing to accept in pursuit of its business objectives. It sets clear boundaries for leadership decisions and defines how much disruption, financial impact, regulatory exposure, and reputational risk the business is prepared to tolerate. This concept is aligned with widely recognized enterprise risk management frameworks such as COSO ERM and ISO/IEC 31000, where risk appetite is defined as a key element guiding strategic decision-making.
In simple terms, risk appetite answers this question:
“What level of information security risk are we prepared to live with as a business?”
This concept is aligned with widely recognized frameworks such as ISO/IEC 31000 and plays a critical role in effective risk governance and decision-making.
But here is the uncomfortable reality:
In many organizations, risk appetite is not clearly defined.
Yet decisions are still being made every day. Which means risk isn’t being managed… it’s being assumed silently.
Why ISO/IEC 27001 Alone Is Not Enough
ISO/IEC 27001 gives organizations a solid structure for managing information security. However, on its own, it does not ensure that security decisions match real business risk. That is where a clearly defined risk appetite framework becomes essential.
Because without it, something critical happens, because the organization defines its real risk appetite through daily decisions. This challenge is increasingly recognized across the industry, where organizations are shifting from control-based approaches to risk-based and decision-driven security models, as highlighted by leading research from Gartner and the World Economic Forum. Consider this, a system goes live with known vulnerabilities to meet a deadline. No one escalates it. No one challenges it. That is risk appetite in action. And it’s exactly in these moments, where decisions are made without clear boundaries, that attackers find their entry point.
Every time a go-live is approved with unresolved vulnerabilities, a vendor is onboarded without full due diligence, a security exception is extended “just this once”; the organization is defining its real risk appetite, whether it admits it or not.
Area | Why ISO/IEC 27001 Alone Is Not Enough |
Security structure | ISO/IEC 27001 sets up the security management system and helps teams identify risks, apply controls, and improve over time. |
Acceptable risk levels | ISO/IEC 27001 does not define how much risk is acceptable. That decision must come from leadership. |
Exceptions | Without risk appetite, exceptions become normalized, and temporary fixes quietly turn into permanent exposure. |
Control effectiveness | Controls can exist without reducing real risk, even when audits are passed. |
Supplier and platform risk | Vendor and platform risks are often accepted by default, without explicit business approval. |
Decision-making | Decisions become reactive, with real exposure only understood after something goes wrong. |
Business alignment | Risk appetite links security controls to real business priorities. |
Leadership value | Risk appetite turns ISO/IEC 27001 from a compliance exercise into a strategic decision-making tool. |
This gap between structure and decision-making is exactly why organizations must go beyond compliance and clearly define information security risk appetite as part of their ISO/IEC 27001 governance approach.
Risk Appetite is a Leadership Decision
One of the most common misconceptions is treating risk appetite as a security exercise. It’s not. Risk appetite is a leadership decision and a core part of enterprise security governance.
If the board isn’t defining it, then risk decisions are being made at the wrong level. Because risk appetite determines how much downtime is acceptable, how much financial loss is tolerable, how much regulatory exposure is acceptable, how much reputational damage the organization can absorb. And more importantly, who has the authority to accept that risk.
Risk Appetite vs Risk Capacity
Many organizations make a critical mistake: they confuse risk appetite vs risk tolerance. Risk appetite is what the organization is willing to accept in pursuit of its objectives, while risk capacity defines what the organization can actually absorb without threatening its viability. These are not the same.
In practice, the gap between them often remains invisible, until it’s too late. Decisions are made based on what feels acceptable in the moment: to meet a deadline, reduce friction or keep operations running. However, these decisions rarely consider the cumulative effect of risk over time.
Because risk doesn’t occur in insolation. It stacks, compounds and interacts with other risks across the organization. What may appear acceptable in a single decision can become unsustainable when repeated or combined with other exposures. What the business is willing to accept isn’t always what it can survive.
This is where many organizations fail, not in identifying risk, but in underestimating its aggregated impact. When risk appetite exceeds risk capacity, the organization is no longer managing risk within safe boundaries, it’s operating beyond its ability to absorb failure. And that’s the point where controlled risk becomes a crisis.
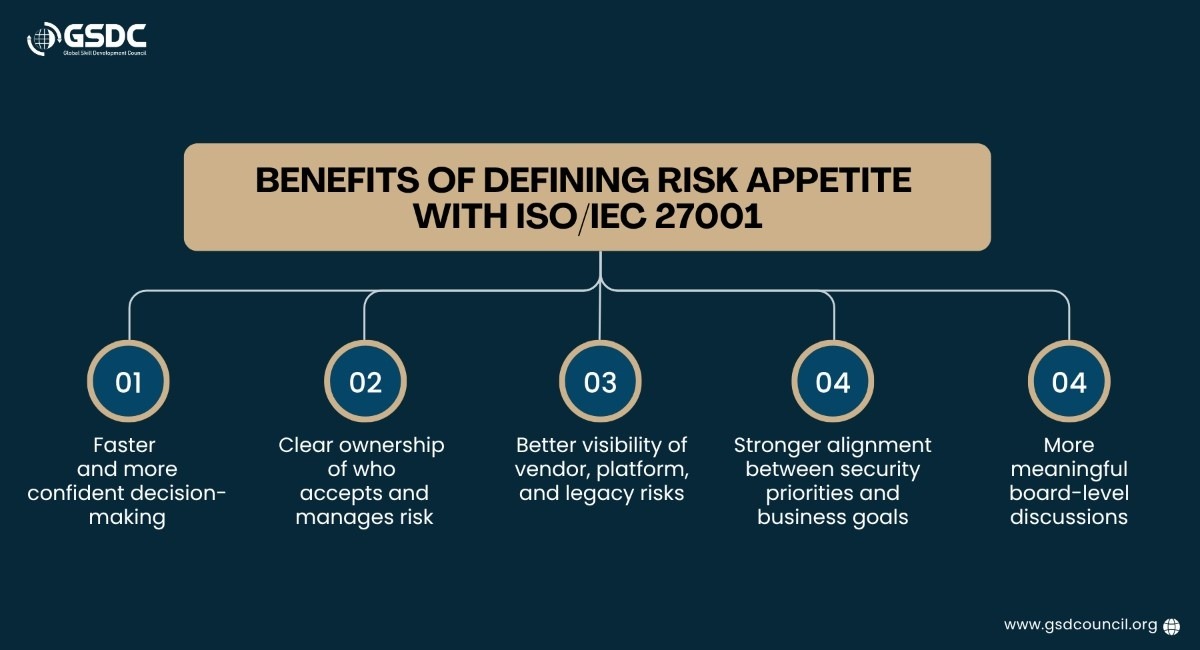
How ISO/IEC 27001 Supports Risk Appetite
ISO/IEC 27001 provides the structured approach to risk management; however, as with many management standards, it doesn’t explicitly define acceptable levels of risk, leaving this responsibility to organizational leadership.
It helps organizations understand their business context.
ISO/IEC 27001 requires organizations to consider their industry, regulatory environment, customers, partners, and critical services. This ensures that risk appetite is based on real business exposure, not generic security assumptions.
It aligns security with business objectives.
Security priorities are linked to strategic goals such as revenue protection, service availability, and customer trust.
It assigns clear risk ownership.
Risk decisions are made by business owners, not only by security teams.
It requires documented risk treatment decisions.
Organizations must clearly record whether risks are accepted, reduced, transferred, or avoided.
It supports continual improvement.
Risk appetite evolves as the business, technology, and threat landscape change.
However, many organizations stop at ISO 27001 compliance, without connecting it to real-world decision-making.
That’s where risk appetite becomes the missing link.
Key Areas Where Risk Appetite Should Be Defined
To make risk appetite practical, organizations must define clear boundaries across the areas that have the greatest business impact.
Operational disruption.
Define how much downtime is acceptable and which services are truly critical.
Financial impact.
Set limits on acceptable loss, including direct and indirect costs.
Regulatory and legal exposure.
Determine tolerance for fines, investigations, and compliance gaps.
Trust and reputation.
Define how much risk the organization is willing to take with customer trust and brand perception.
These decisions directly influence an organization’s overall security posture management, especially in cloud-driven environments where cloud security posture management is critical.
Turning Risk Appetite Into Action
Risk appetite should not sit in a policy document. It must guide real, day-to-day decisions, because over time risk doesn’t disappear, it accumulates. And accumulated risk isn’t neutral, it becomes an attack surface. To make it real:
Define non-negotiable security requirements.
Set clear security rules that cannot be overridden, especially for critical systems, sensitive data, identity controls, backups, and access to key platforms. These non-negotiables create firm boundaries that prevent high-impact risk from being introduced through operational decisions.
Set measurable thresholds.
Define quantifiable limits that clearly indicate when risk moves from acceptable to unacceptable, such as acceptable downtime, recovery time objectives, data loss thresholds, and service availability targets. These thresholds make risk tangible and enable both technical and business teams to act consistently and in a timely manner.
Establish clear escalation and approval rules.
Define and document who must be notified and who has the authority to approve decisions when thresholds are exceeded. This ensures that significant risks are managed at the appropriate leadership level and prevents informal or ungoverned decision-making.
Time-box and review security exceptions.
Require all exceptions to have a defined expiry date and a formal review process before renewal. This prevents short-term workarounds from becoming permanent exposures and reduces the silent accumulation of risk over time.
Embed risk appetite into key processes.
Integrate risk appetite into key business and technology processes such as change management, cloud, vendor onboarding and incident response, so it directly influences day-to-day decisions. This ensures consistent risk management aligned with strategic priorities rather than isolated or reactive actions.
This is how an information security governance framework becomes operational - not theoretical.
Common Mistakes to Avoid
Organizations often struggle with risk appetite because it is treated as a document instead of a leadership tool that guides real decisions.
Using vague labels like “low, medium, high.”
These terms do not translate into real business impact, financial exposure, or operational consequences. During a crisis, they provide no guidance on what actions to take or who should decide.
Defining it once and never reviewing it.
As the business, technology, vendors, and threat landscape change, risk appetite must be reviewed and updated. A static risk appetite quickly becomes disconnected from reality.
Leaving ownership only with security teams.
Risk appetite must be set and owned by leadership and business owners. Without this ownership, risk decisions lack accountability and strategic alignment. Security teams should support the process, but they should not be the only ones defining acceptable risk.
Not linking it to real operational decisions.
If risk appetite does not influence change approvals, cloud architecture, vendor onboarding, or exception handling, it is not being used in practice. Effective risk management requires embedding it into real workflows and decision-making processes.
Treating exceptions as routine.
Frequent or unmanaged exceptions gradually become the norm, increasing exposure over time. Without strict review and expiry, exceptions quietly redefine the organization’s true risk posture.
Effective risk appetite is a leadership responsibility that must be reviewed, enforced, and embedded into daily business and technology decisions, not just documented.
These gaps weaken effective cyber risk governance and lead to silent risk accumulation.
Strengthen Your Risk Leadership
Defining risk appetite requires more than frameworks; it needs the right skills and perspective. The Global Skill Development Council (GSDC) helps professionals go beyond compliance with practical, real-world expertise.
The Certified ISO 27001:2022 Lead Auditor certification equips you to assess, audit, and align security controls with real business risk. It helps turn ISO/IEC 27001 from a compliance exercise into a strategic advantage.

Conclusion
ISO/IEC 27001 provides the foundation, but a foundation alone doesn’t define direction. Risk appetite does. It determines what the organization is willing to accept, what it must prevent, and who has the authority to decide. Without it, controls lose context, exceptions must be normalized, and risk is no longer governed, it’s accumulated.
Risk doesn’t disappear. It compounds over time, hides behind operational decisions, and only becomes visible when the impact is unavoidable. In many organizations, this accumulation happens silently, embedded in everyday trade-offs that were never challenged or escalated.
Many organizations believe they are operating within acceptable risk levels. But in reality, they’re operating beyond what they can absorb. Because the real issue isn’t the presence of the risk, it’s the misalignment between risk appetite and risk capacity. When the gap is ignored, risk doesn’t remain controlled. It escalates, compounds and eventually exceeds the organization’s ability to respond.
If risk appetite isn’t clearly defined, then risk isn’t being managed. It’s being assumed, normalized, and progressively built into the organization’s operating model. And in the silence, exposure continues to grow until it’s no longer a risk discussion, but a business crisis.
Because attackers don't wait for controls to fail. They look for gaps in how risk is defined, accepted and ignored. Because in the absence of clear boundaries, someone else will define them, your attackers.
Subscribe to Our Newsletter
Stay up-to-date with the latest news, trends, and resources in GSDC
Related Certifications
Stay up-to-date with the latest news, trends, and resources in GSDC
If you like this read then make sure to check out our previous blogs: Cracking Onboarding Challenges: Fresher Success Unveiled
Not sure which certification to pursue? Our advisors will help you decide!