Managing IT Suppliers and Vendors Under ISO 20000

Written by Livia Clozel
- The Expanding Landscape of IT Suppliers
- Why Vendor Risk Mapping Is Essential
- The Role of Contracts in Vendor Governance
- Managing Cloud and Infrastructure Risks
- Challenges with SaaS Vendor Changes
- Managing Cross-Border Data Transfers
- Vendor Support and Operational Capacity Risks
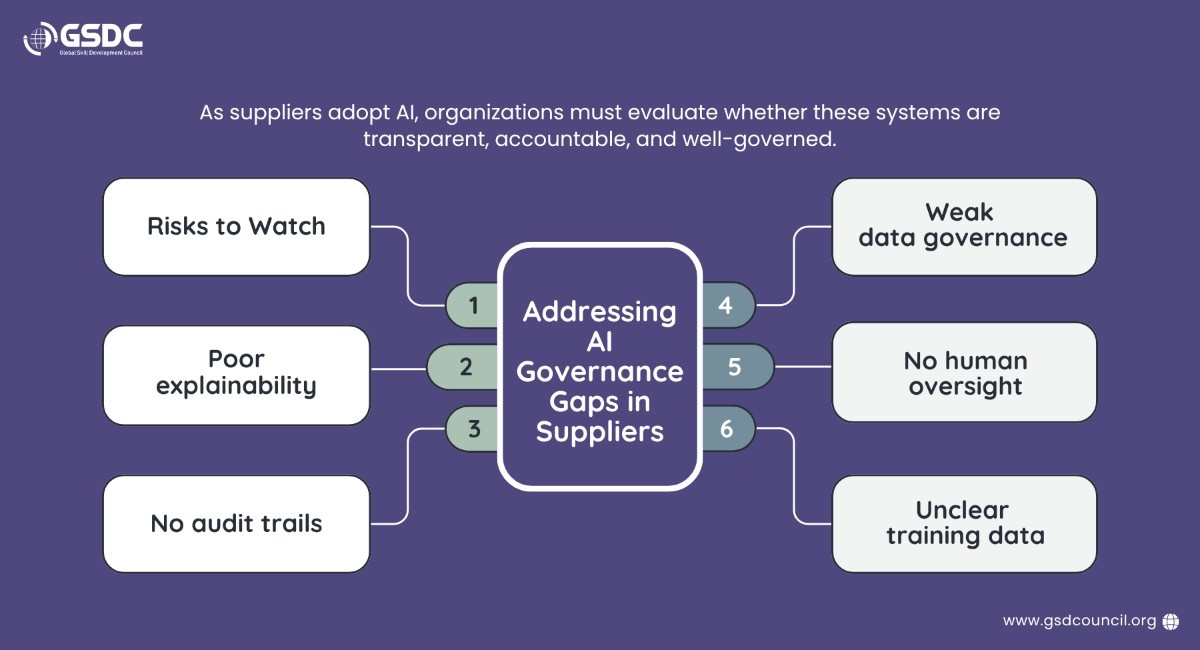
- Addressing AI Governance Gaps in Suppliers
- Managing Global and Systemic Risks
- How Certificate Help Here?
- The Importance of Integrated Governance
- Conclusion
In today’s digital ecosystem, organizations rely heavily on IT suppliers and vendors to deliver services, infrastructure, software, and technical expertise. From cloud providers and SaaS platforms to freelancers and open-source components, modern IT services often depend on multiple external partners. While these partnerships accelerate innovation and scalability, they also introduce significant risks if not managed properly, making supplier management a critical function for every organization.
The international service management standard ISO 20000 provides a structured framework for organizations to manage IT services effectively, including the governance of suppliers and vendors. Effective supplier management under ISO 20000 helps organizations improve service reliability, maintain regulatory compliance, and build stronger operational resilience. It also supports better performance management vendor practices by ensuring suppliers consistently meet agreed service expectations and business objectives.
In a recent webinar titled “Managing IT Suppliers and Vendors Under ISO 20000,” the session highlighted the growing challenges organizations face in supplier governance and emphasized the importance of supplier risk assessment and ongoing vendor risk assessments to identify, evaluate, and mitigate third-party risks.
This blog summarizes the key insights from the webinar and explains how organizations can strengthen supplier management, improve vendor oversight, and implement effective supplier risk assessment strategies using ISO 20000 principles.
The Expanding Landscape of IT Suppliers
Modern IT environments are built on complex supply chains. Organizations today work with a wide range of external partners.
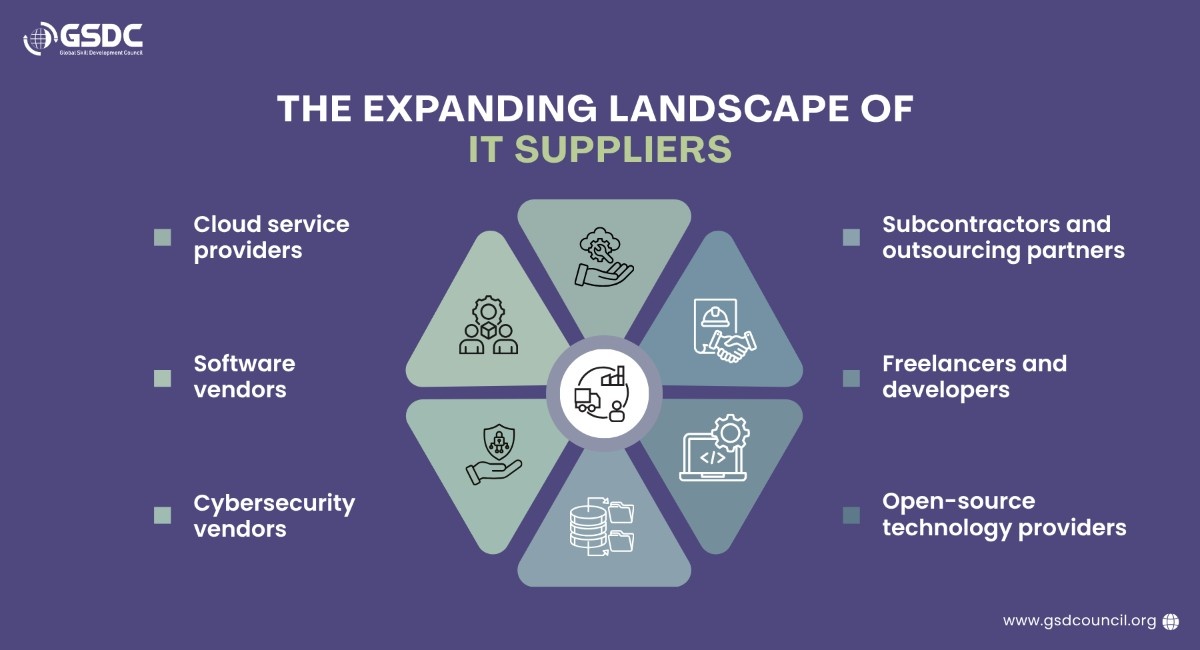
Because of this complexity, companies often lose visibility into the risk exposure introduced by suppliers. A weak vendor security posture, poor contractual agreements, or insufficient governance can become a major vulnerability.
Under ISO/IEC 20000, supplier management is not just about selecting vendors; it involves continuous monitoring, risk assessment, and alignment with organizational policies.
Why Vendor Risk Mapping Is Essential
One of the most important lessons from the webinar was the need for vendor risk mapping before onboarding any supplier.
Many organizations mistakenly treat technical solutions as “plug-and-play.” In reality, every vendor integration introduces risks related to:
- Security vulnerabilities
- Data privacy exposure
- Operational dependencies
- Compliance requirements
- Contractual obligations
Before deploying any vendor solution, organizations must conduct detailed assessments that include:
- Reviewing vendor policies and documentation
- Evaluating security and privacy controls
- Analyzing operational risks
- Understanding integration dependencies
This proactive approach helps organizations identify potential problems before the system goes live.
The Role of Contracts in Vendor Governance
Contracts play a critical role in supplier management. Poorly structured agreements often leave organizations exposed to operational or legal risks.
Many companies sign vendor contracts that contain strong obligations for the client but weak protections for the organization. Some common issues include:
- Weak or unclear Service Level Agreements (SLAs)
- Lack of IT-specific clauses
- Undocumented integrations
- Vendor lock-in risks
- Absence of data portability clauses
- No defined penalties for service failure
To address these gaps, organizations should ensure that vendor contracts include clear provisions for:
- Data ownership and portability
- Exit strategies and transition plans
- Security and privacy requirements
- Incident response responsibilities
- Compliance obligations
Strong contracts ensure that suppliers remain accountable for their services and responsibilities.
Managing Cloud and Infrastructure Risks
Cloud computing has become a core component of modern IT services, but it also introduces operational risks.
Cloud-related risks discussed in the webinar include:
- Regional cloud failures
- Data residency restrictions
- Infrastructure overload
- Latency spikes
- Geopolitical restrictions affecting cloud regions
For example, an organization using cloud infrastructure from Amazon Web Services must understand where data is stored and how regional outages could affect service availability.
To mitigate these risks, organizations should implement:
- Multi-region architectures
- Hybrid cloud strategies
- Data localization planning
- Business continuity testing
These strategies improve resilience and ensure continuity during infrastructure disruptions.
Challenges with SaaS Vendor Changes
Another major issue organizations face is the rapid evolution of Software-as-a-Service (SaaS) platforms.
SaaS vendors frequently release updates, new models, or feature changes that may disrupt existing integrations. In some cases, vendors may:
- Remove important features
- Force upgrades
- Modify APIs
- Change pricing or service models
These changes can break operational workflows even without a cyberattack.
To prevent disruptions, organizations should include change control clauses and regression testing requirements in vendor agreements.
Managing Cross-Border Data Transfers
Data privacy is a critical aspect of vendor management, especially when organizations operate globally.
When vendors process personal data, companies must comply with privacy regulations such as the General Data Protection Regulation.
Organizations must clearly map:
- Where data is stored
- Where it is transferred
- Which jurisdictions apply to the data
For example, a cloud provider may operate data centers in multiple countries. Even if the organization operates in Europe, the vendor’s infrastructure could involve data transfers to other jurisdictions.
Companies should conduct Transfer Impact Assessments (TIAs) to evaluate privacy risks and ensure compliance with regulatory requirements.
Vendor Support and Operational Capacity Risks
Another often overlooked risk involves vendor support capacity.
Due to financial pressures or organizational restructuring, vendors may quietly reduce support teams or operational resources. This can lead to:
- Slower patching cycles
- Increased recovery times
- Reduced monitoring capabilities
- Lower service reliability
To mitigate these risks, organizations should define minimum support standards and operational capacity requirements in vendor contracts.
Regular supplier audits and performance monitoring also help ensure vendors maintain the expected level of service.
Addressing AI Governance Gaps in Suppliers
Many vendors are rapidly adopting artificial intelligence technologies, but not all organizations have proper governance in place.
Potential risks in supplier AI systems include:
- Lack of explainability in AI decisions
- No audit trails for AI outputs
- Poor dataset governance
- Absence of human oversight
- Unclear training data sources
To address these concerns, organizations should request transparency from vendors regarding their AI models.
The emerging AI governance framework ISO/IEC 42001 provides guidelines for responsible AI management and governance.
Organizations can use this framework to assess whether vendor AI systems meet appropriate governance standards.
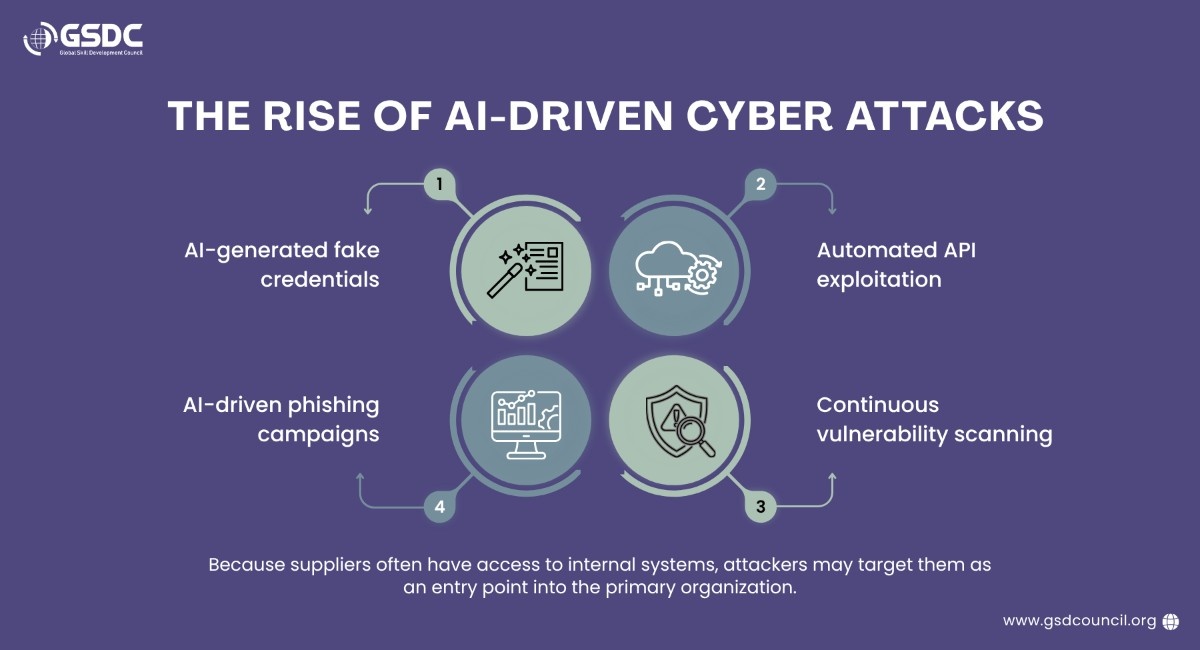
Managing Global and Systemic Risks
Vendor risks are no longer limited to technical issues. Organizations must also consider broader global factors, including:
- Financial instability of vendors
- Geopolitical conflicts
- Climate disruptions
- Cyber threats
- Supply chain dependencies
These risks often converge, creating complex failure scenarios.
To prepare for such events, organizations can implement advanced risk management techniques such as:
- Scenario modeling
- Stress testing
- Third-party risk management (TPRM) frameworks
- Cyber resilience assessments
Vendor governance must therefore be multi-disciplinary, involving IT, security, legal, compliance, and operational teams.
How Certificate Help Here?
The GSDC Certified ISO 20000 Lead Implementer helps professionals gain practical knowledge of implementing IT Service Management Systems (ITSMS) based on ISO 20000:2018 standards. It strengthens skills in service planning, process improvement, risk management, compliance, and continual service enhancement. This certification is valuable for IT managers, consultants, auditors, and service professionals who want to improve service quality and align IT operations with global best practices. It also boosts professional credibility, increases job opportunities, and supports career growth in IT service management.
Overall, GSDC’s certification equips professionals to lead ISO 20000 implementation confidently and effectively in modern organizations.
Benefits:
The Importance of Integrated Governance
One of the key messages from the webinar was that supplier lifecycle management cannot be handled by a single department. Effective governance across the vendor management lifecycle requires collaboration among multiple business functions to ensure suppliers are assessed, approved, and monitored properly.
This includes close involvement from:
- IT service management teams
- Cybersecurity teams
- Legal departments
- Data Protection Officers (DPOs)
- Compliance and risk teams
Organizations should ensure that vendor onboarding takes place only after all relevant stakeholders have reviewed and approved the supplier. This cross-functional approach strengthens iso vendor management practices, improves vendor performance, and helps organizations align with the requirements of ISO 20000 certification.
By embedding collaboration into the supplier lifecycle management process, organizations can identify and address risks early before they impact service quality, security, or overall business operations.
Conclusion
Managing IT suppliers and vendors has become increasingly complex in the modern digital landscape. Organizations rely on external partners for critical services, making supplier lifecycle management and a well-defined vendor management lifecycle essential for maintaining service quality, reducing dependency risks, and ensuring business continuity. However, this reliance also introduces operational, security, and compliance challenges that must be managed proactively.
By adopting the structured framework provided by ISO/IEC 20000, organizations can build a robust iso vendor management program that includes risk assessments, strong contracts, continuous monitoring, and cross-functional collaboration. These practices also support better vendor performance by ensuring suppliers are regularly evaluated against service expectations, contractual obligations, and organizational goals. In addition, aligning with these best practices can support organizations pursuing ISO 20000 certification by demonstrating effective control over third-party service providers.
Ultimately, proactive supplier management is far more effective than reacting to incidents after they occur. Organizations that invest in strong governance across the vendor management lifecycle will improve service reliability, reduce operational risk, strengthen vendor performance, and enhance their overall IT service management capabilities.
Related Certifications
Frequently Asked Questions
Stay up-to-date with the latest news, trends, and resources in GSDC
If you like this read then make sure to check out our previous blogs: Cracking Onboarding Challenges: Fresher Success Unveiled
Not sure which certification to pursue? Our advisors will help you decide!